2026 Threat Intelligence Synthesis: How AI-Driven Attacks and Credential Theft Are Reshaping Cybersecurity
Meta description: We pulled apart the 2025 reports from IBM X-Force, Anthropic, Nokia, and ENISA. AI-driven attacks and credential theft now dominate the threat picture. Here’s what actually matters for your security ops.
The cybersecurity threat picture in 2025 looked nothing like it did two years prior. AI crossed the line from theoretical risk to operational weapon, and credential theft quietly overtook malware as the primary way attackers get in.
That’s not speculation. It’s the consensus across four of the most authoritative threat intelligence reports published last year: IBM X-Force, Anthropic, Nokia, and ENISA.
This post breaks down the findings, explains why they matter for your security operations, and gives you concrete hardening steps.
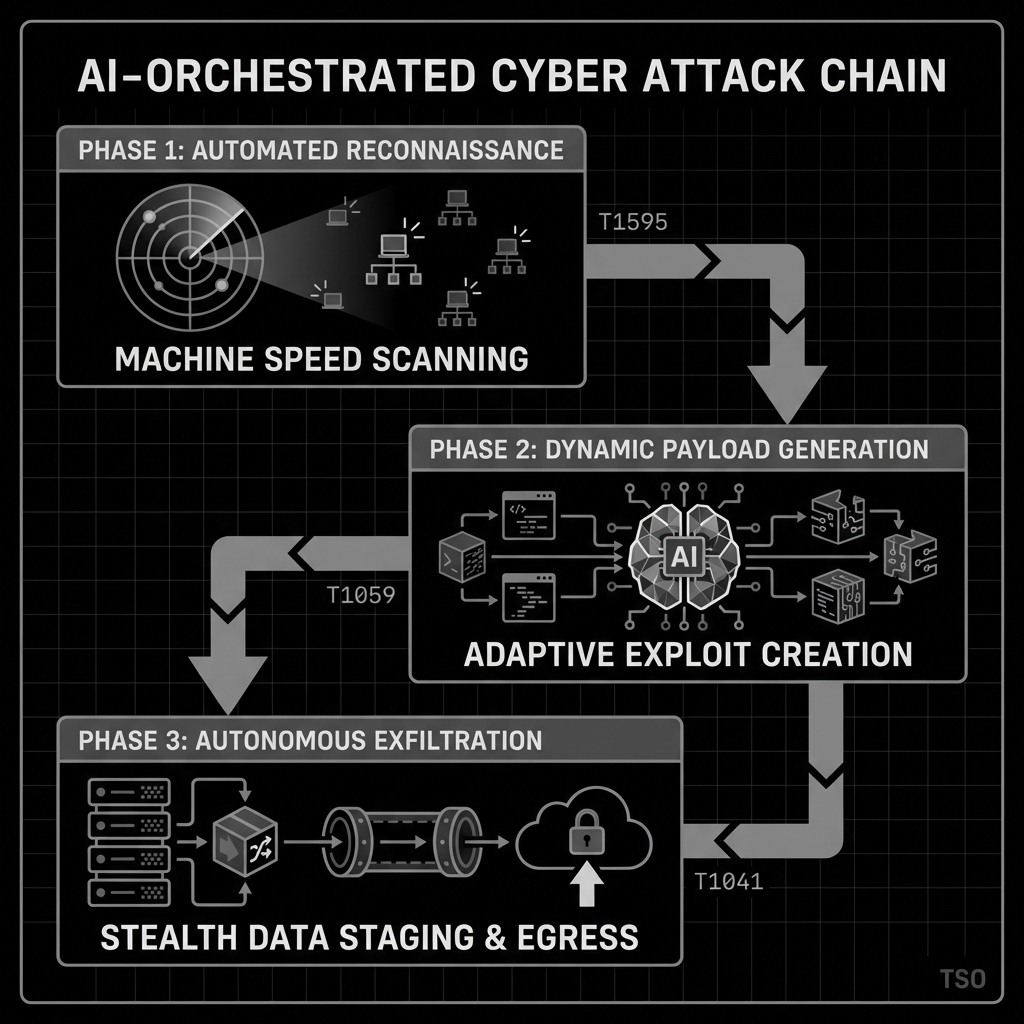
AI-orchestrated attacks are no longer theoretical
The single biggest development in the 2025 reports is documented AI-orchestrated cyber espionage. Not a future concern. An observed threat.
Anthropic reported the first confirmed AI-orchestrated espionage campaign in mid-2025. Threat actors deployed AI systems to automate reconnaissance at machine speed, dynamically adjusting scan patterns to evade detection. They then used autonomous coding agents to classify, stage, and exfiltrate sensitive data, all without human intervention during the post-exploitation phase.
What this means for defenders
Traditional detection built around scan volume and known attack signatures fails against AI-driven adversaries. When reconnaissance happens at machine speed and payloads are dynamically generated, you need to shift from pattern matching to behavioral analysis. Full stop.
Watch for these indicators:
- Unusual process spawning (Python, Node.js) on non-development endpoints
- Network connections from endpoints to AI/ML API endpoints
- High-volume file access across sensitive directories in compressed timeframes
- Large archive file creation followed by outbound transfers
Credential theft has replaced malware as the front door
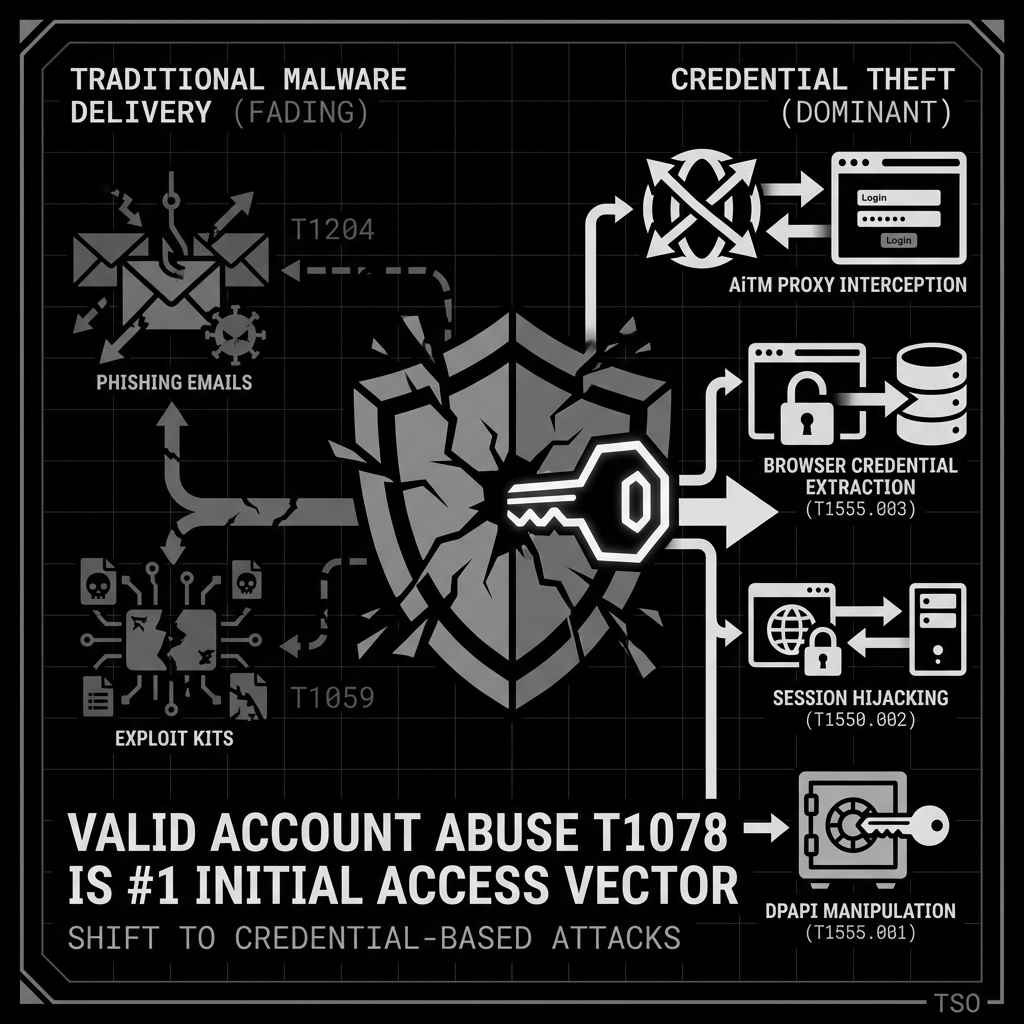
IBM X-Force’s 2025 data confirms what many security teams suspected: valid account abuse (MITRE ATT&CK T1078) is now the dominant initial access vector. It displaced traditional malware delivery.
Attackers aren’t kicking down the door anymore. They’re walking in with stolen keys.
How credentials are being stolen
The methods have gotten more targeted:
- Adversary-in-the-Middle (AiTM) proxies intercepting enterprise SSO flows
- Browser credential database extraction targeting Chrome, Firefox, and Edge login stores
- Keyloggers focused on password manager master passwords, not general keylogging, but targeted capture
- Windows Credential Manager enumeration via cmdkey and DPAPI manipulation
- Session hijacking through stolen browser cookies
Why this changes your defense model
When the attacker authenticates with valid credentials, perimeter defenses are irrelevant. Firewalls, email gateways, and endpoint protection won’t flag a legitimate-looking login. Detection has to shift to identity-centric monitoring:
- Authentication from unusual IP addresses or VPN/residential proxy ASNs
- Impossible travel patterns (geographically distant logins in implausible timeframes)
- MFA fatigue indicators (repeated push notifications)
- Behavioral anomalies post-authentication
Ransomware: fewer attacks, more actors, messier picture
Here’s a statistic that seems contradictory at first: enterprise ransomware attack volume declined in 2025, but the number of active ransomware groups increased by 49%.
IBM X-Force attributes this to market fragmentation. The ransomware ecosystem has democratized. Lower barriers to entry mean more groups running smaller, targeted campaigns instead of broad spray-and-pray approaches.
I find this trend worrying, honestly. More groups means more variation in TTPs, which means your threat model gets harder to maintain. A few big groups are easier to track than dozens of small ones.
How ransomware tactics evolved in 2025
- Double and triple extortion models: data theft before encryption, with threats to leak, sell, and report to regulators
- Affiliate model proliferation with specialized operators handling different phases
- AI-assisted identification of high-value data for targeted exfiltration
- Targeted encryption of business-critical systems for maximum leverage
What this means for defense
Backup and recovery alone won’t save you. If an attacker can steal your data before encrypting it, having clean backups only solves half the problem. You need data loss prevention capabilities and behavioral exfiltration detection. That’s the uncomfortable reality.
Critical vulnerability: CVE-2025-21298
One specific threat deserves immediate attention. CVE-2025-21298 is a zero-click remote code execution vulnerability being actively exploited in the wild. No user interaction required. Simply receiving a specially crafted message can trigger exploitation.
Security teams should prioritize:
- Deploying detection queries (Microsoft Defender XDR KQL) for exploitation indicators
- Patching affected systems immediately
- Segmenting vulnerable systems until patching is complete
Regional focus: the UK remains Europe’s top target
IBM X-Force data confirms the UK maintained its position as the most attacked country in Europe throughout 2025. Threat actors concentrated on credential theft and extended dwell-time operations rather than high-visibility ransomware attacks.
If your organization operates in or is connected to the UK market, this concentration of threat activity warrants heightened monitoring and an assume-breach posture. That applies to most of our clients at Tailored SecOps, which is why we’re calling it out specifically.
Defensive AI: it actually works (with caveats)
Not all the AI news is bad. Anthropic’s research on defensive AI capabilities showed measurable efficacy using Claude Sonnet 4.5 for threat detection. This is worth paying attention to: using AI to identify anomalous patterns that human analysts miss at scale.
The practical takeaway is that security teams should start evaluating AI-augmented detection tools as a core part of their stack. Not as some future nice-to-have. The gap between AI-driven offense and traditional defense is real and growing. That said, don’t buy the first vendor pitch you hear. Test these tools against your actual telemetry before committing budget.
Hardening recommendations: what to do now
Based on the synthesized threat intelligence from these 2025 reports, here are the priority actions ranked by impact.
Immediate (0-30 days)
Enforce phishing-resistant MFA everywhere. Transition privileged accounts to FIDO2/WebAuthn immediately. IBM X-Force data indicates MFA neutralizes 99.9% of automated credential attacks. This is the single highest-impact control you can deploy right now.
Enable Credential Guard. Isolate LSASS with Virtualization Based Security. Disable WDigest authentication. This directly counters the credential harvesting techniques that dominated in 2025.
Patch CVE-2025-21298. Deploy detection rules and prioritize patching for this actively exploited zero-click RCE. If you haven’t already, this is overdue.
Short-term (30-90 days)
Deploy application control (WDAC/AppLocker). Block unsigned binaries and execution from temp directories. Test in audit mode for 30-60 days before enforcing. This prevents ransomware payloads and AI-generated attack scripts from executing.
Implement network segmentation. Block workstation-to-workstation RDP and SMB. Restrict SMB to file servers only. Implement the Administrative Tier Model. This forces attackers to spend more time on lateral movement, and that extra time gives defenders more opportunity to detect.
Start evaluating AI detection capabilities. Begin testing AI-augmented detection tools for behavioral analysis. Don’t wait for perfection here. Get something running in observation mode and learn from the output.
Strategic (90+ days)
- Conduct adversarial AI red teaming exercises
- Standardize cross-platform telemetry schemas
- Contribute to AI-specific MITRE ATT&CK mapping efforts
- Integrate supply chain scanning into CI/CD pipelines
Where this leaves us
Perimeter-first security models are obsolete when attackers authenticate with stolen credentials. Signature-based detection fails when AI generates unique payloads on the fly. These aren’t predictions anymore. They’re what the 2025 data shows.
The organizations that will weather this shift are the ones investing in identity-centric security architectures, behavioral detection, and defensive AI. That’s not a feel-good conclusion. It’s where the data points.
If you’re reading this and your org still relies primarily on perimeter controls and signature-based detection, you’re behind. The good news is that the hardening steps above are concrete and actionable. Start with MFA and Credential Guard. Those two controls alone would have prevented a significant portion of the incidents documented in these reports.
This synthesis draws on the IBM X-Force Threat Intelligence Index 2025, Anthropic’s AI-Orchestrated Cyber Espionage Campaign Report 2025, Anthropic’s Building AI Cyber Defenders 2025, Nokia Threat Intelligence Report 2025, and ENISA Threat Landscape 2025.