The Belgian pentest market in 2026
Belgium sits at the center of European cybersecurity regulation. Brussels hosts the EU institutions that write the rules. ENISA coordinates cross-border incident response. And Belgian companies, from financial services firms near the Rue de la Loi to manufacturing operations in Flanders, face compliance requirements from NIS2, GDPR, DORA, and sector-specific frameworks that all demand some form of security testing.
The result: a growing market for penetration testing services, and a growing problem. Not all of it is worth paying for.
There are genuine red team operations that find the vulnerabilities your automated scanners miss. And there are firms running Nessus, reformatting the output into a PDF, and calling it a pentest. The difference matters. If you are evaluating penetration testing companies in Belgium, this post covers what to look for.
What penetration testing actually means
The term gets used loosely. A vulnerability scan is not a penetration test. A compliance checkbox assessment is not one either. Both have their place, but they solve different problems.
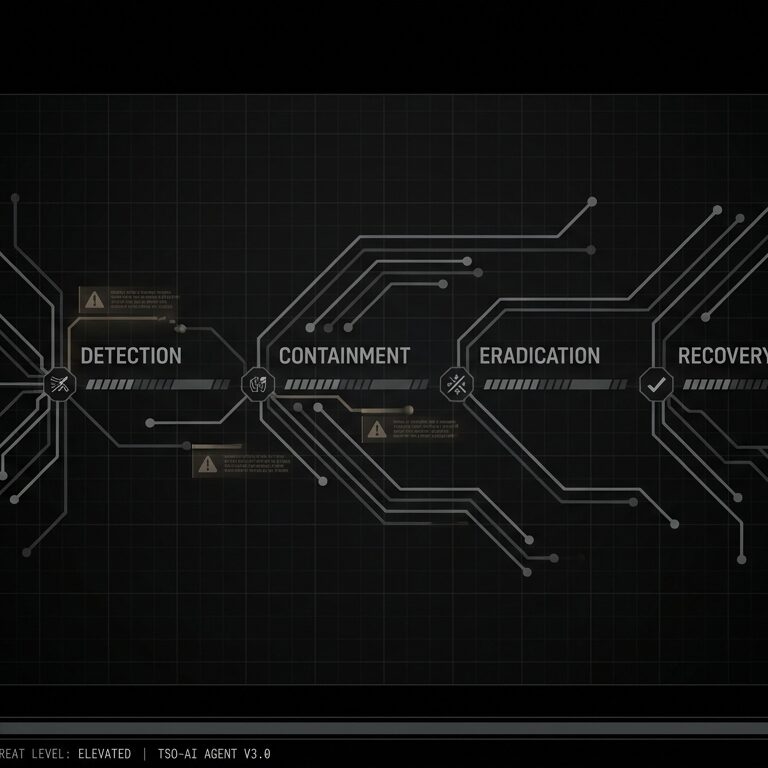
A penetration test is a controlled attempt to break into your systems the way a real attacker would. That means:
- Reconnaissance and scoping. Understanding the target environment, mapping the attack surface, figuring out what matters.
- Manual testing. A skilled tester probing for weaknesses that automated tools miss: business logic flaws, authentication bypasses, chained vulnerabilities that only make sense when a human connects the dots.
- Exploitation. Proving a vulnerability is real by actually exploiting it, not just flagging a theoretical risk.
- Reporting with context. Explaining what was found, what an attacker could do with it, and how to fix it, prioritized by actual business impact rather than generic CVSS scores.
Red team assessments go further. A red team engagement simulates a full adversarial campaign: initial access, lateral movement, persistence, data exfiltration. The goal is to test whether your detection and response capabilities hold up, not just find individual bugs. In Belgium, red team assessments increasingly need to account for hybrid environments spanning on-prem infrastructure, cloud services, and OT networks in industrial settings.
What separates good penetration testing from bad
Methodology depth
Ask about methodology. A credible firm will walk you through their approach in detail. They should reference established frameworks: OWASP Testing Guide for web applications, PTES for general penetration testing, TIBER-EU for threat-led red teaming (particularly relevant for Belgian financial institutions under NBB oversight).
If the methodology conversation is vague, or if the answer is basically “we run our tools and report what they find,” that tells you something.
Tester expertise
The quality of a penetration test depends almost entirely on who does the work. Certifications matter as a baseline (OSCP, OSWE, CREST, GXPN), but demonstrated experience matters more. Ask about the types of environments they have tested. Ask for anonymized case studies. Ask about the hardest bug they found recently and how they found it.
Web application security testing in Belgium has specific nuances. Many Belgian organizations run multilingual applications (Dutch, French, German, English) with complex role-based access controls. E-government integrations (eID, CSAM authentication) introduce attack surface that generic testing methodologies don’t cover well.
Reporting quality
The report is the deliverable. If it reads like machine output with no human analysis, the test was probably automated with minimal human involvement.
Good reports include an executive summary that a non-technical stakeholder can act on, technical details sufficient for developers to reproduce and fix each finding, risk ratings calibrated to your specific environment rather than generic severity scores, remediation guidance that accounts for your technology stack, and evidence: screenshots, request/response pairs, proof-of-concept code.
Post-test support
A firm that delivers a report and disappears is not a partner. Look for teams that offer retest windows, answer developer questions during remediation, and keep enough context about your environment to provide continuity across engagements.
The Belgian and European context
Regulatory pressure
Belgian organizations operate under overlapping regulatory frameworks that either require or strongly incentivize penetration testing.
NIS2 applies to essential and important entities. Belgium’s transposition through the CCB (Centre for Cybersecurity Belgium) requires appropriate security testing as part of risk management measures. GDPR Article 32 requires “a process for regularly testing, assessing and evaluating the effectiveness of technical and organisational measures.” Penetration testing is the most direct way to demonstrate this. DORA mandates threat-led penetration testing for significant financial entities, following TIBER-EU methodology. On top of those, sector-specific requirements in healthcare (eHealth platform compliance), energy (ACER guidelines), and government (FedICT security requirements) add their own layers.
Choosing a penetration testing company that understands the Belgian regulatory landscape means the output of their work directly supports your compliance obligations. The test is also your evidence when a regulator comes knocking.
Language and proximity
This is practical, not patriotic. When findings need to be discussed with development teams in Ghent, management in Brussels, and infrastructure teams in Liège, having testers who can communicate in Dutch, French, and English removes friction. Same time zone means findings get discussed and remediated faster.
For red team assessments that include physical security testing or social engineering, local knowledge and language fluency are not optional.
Data residency and sovereignty
Belgian and European data protection requirements mean you need to know where your test data goes. If your penetration testing provider routes traffic through infrastructure outside the EU, or if their reporting platform stores findings on US-hosted servers without adequate safeguards, you may have a compliance problem layered on top of whatever vulnerabilities they find.
What to ask before signing
Before engaging a penetration testing company in Belgium, these questions cut through the sales pitch:
- Who will actually do the testing? Not the account manager. The person with the keyboard. What is their background?
- What is your methodology for our specific technology stack? Generic answers are a red flag.
- How do you handle sensitive data encountered during testing? This matters for GDPR compliance.
- Can you provide references from similar engagements? Ideally in the same sector and regulatory environment.
- What does your report look like? Ask for a redacted sample.
- How do you scope and price? Time and materials with a clear scope definition is usually more honest than fixed price “unlimited testing.”
- What happens when you find something critical mid-engagement? The answer should involve immediate notification, not waiting for the final report.
Cybersecurity consulting beyond the test
Penetration testing is one engagement. The organizations getting the most value from it treat it as part of their broader security program. The testing firm should understand how their findings connect to your risk register and your compliance obligations.
Cybersecurity consulting in Europe increasingly means helping organizations figure out where technical security and regulatory compliance overlap. A penetration test that finds an SQL injection is useful. A penetration test that finds an SQL injection, maps it to your GDPR Article 33 notification obligations, and helps you assess whether personal data was at risk is far more useful.
So what do you actually do with this?
The Belgian penetration testing market has more players than it did five years ago. Regulatory pressure from NIS2, GDPR, and DORA drives demand, and AI-augmented tools are expanding what testers can cover in a single engagement. But none of that changes the fundamentals: the quality of a penetration test comes down to the people doing it.
Find testers who know what they are doing, who can explain their methodology without hiding behind buzzwords, and who understand the regulatory environment you operate in. That narrows the field quickly.
If you are evaluating penetration testing or red team assessment services for your Belgian or European organization, get in touch.