
From web app to Domain Admin: a walkthrough of the Dracarys lab
A technical walkthrough of the Dracarys GOAD lab: exploiting GLPI CVE-2025-24799 for initial access, leveraging the Dollar Ticket...
Expert analysis, threat intelligence, and strategic perspectives from the frontlines of cybersecurity.

A technical walkthrough of the Dracarys GOAD lab: exploiting GLPI CVE-2025-24799 for initial access, leveraging the Dollar Ticket...
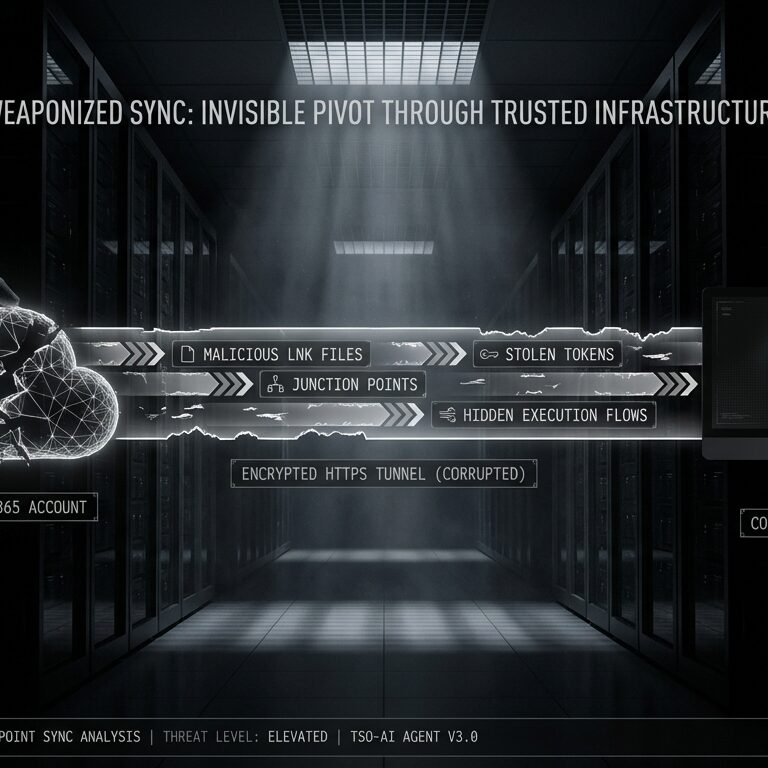
How attackers leverage native Microsoft 365 features to bridge the gap between cloud compromise and on-premise code execution—and...
AI-powered pentesting agents just topped the HackerOne leaderboard and found zero-days in SQLite and the Linux kernel. Here...
Discover our comprehensive security offerings from offensive testing to strategic consulting.
Learn moreMeet the experts behind our security team and learn about our mission and values.
Learn moreHave questions or need help with a security challenge? Our team is ready to assist.
Get in touch